When researcher Yvonne Volkart (University of Applied Sciences and Arts Northwestern Switzerland) was making a stop over in Linz on her way to Vienna we took the opportunity to meet her and hear more about her research “Times of Waste“. Besides learning a bit more about the interdisciplinary methodologies of the research group at the Institute of experimental Design and Media we had an exchange of thoughts around e-waste specially focusing on Yvonne’s topic “biography of a smartphone”.
In Agbobloshie we observed vast amounts of mobile phones amongst the e-waste, but smart phones were still rarely recycled there. According to Yvonne the reason might be that we tend to hold on to our phones for a long time. Even if we do not use them they tend to linger some where in a shoe box till they are thrown away e.g. in connection with moving apartments. At least in Switzerland (where Yvonne’s research is focused on) most of the phones are given to recyclers, but the access to information of what happens to the phones after this is much harder to retain.
We observed that also in Austria there are a number of ways to get rid of an old phone and even feel good about it. For example tolle-tonne.at promises to take care of your old mobile phone and even children with heart conditions will benefit from this. On their website one is secured that the data is deleted from the phones before they are given forward, but the unmonitored cardboard boxes that are used to collect the devices do not convince us to leave a mobile phone with undeleted data there. On the websites there is little information about partners or further strategies of how the phone are reused or recycled. As stated in the “Time of Waste” research abstract “Waste is hence considered as a “new resource”, dynamic and transformable.” also Yvonne is focusing in her ongoing research to map how the business of recycling is formed in Switzerland. According to her much of the smart phones are still re-purposed and reuse, making it extremely important to trust that the data on them is actually deleted.
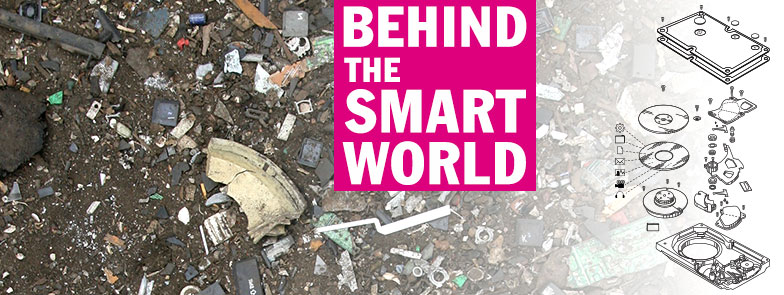
While in first hand it seems easy to delete the data on a smart phone just by using the ‘factory reset’ option, there seems to be a reason to doubt its effectiveness. And there seems to be a number of guides and software for DIY recovery as well. This combined to the complex re-use and recycling practices that unfolding in Yvonne’s research makes it interesting to think about the smart phone as storage mediums with similar problematics as with the 22 hard-drives bought at Agbobloshie. Both with hard-drives and smartphones the hardware can be seen as a resource for “urban mining” regain reusable raw materials out of waste (“Time of Waste” research abstract), and the data breach can become a source of data mining regain of material for potential (ab)use.
Another interesting point coming out of Yvonne’s research was a conclusion, that compare to the amount of waste generated of home electronics such as fridges or televisions when looking into the amount of e-waste produced the mobile phones are relatively small. Yet the amount of residue produced in the production of a new phone in much larger. The amount of waste in production of new electronics is something that Jennifer Garbys talks about in her book ‘Digital Rubbish’ specially focusing on the microchip, a component found in many of our electronics also in our mobile phones:
“To produce a two gram memory microchip, 1.3 kilograms of fossil fuels and materials are required. In this process, just a fraction of the material used to manufacture microchips is actually contained in the final product, with as much as 99 percent of materials used discarded during the production process. Many of these discarded materials are chemicals—contaminating, inert, or even of unidentified levels of toxicity.”
Therefore from an ecological perspective it is not enough to look at affects of our technologies at the end of the lifespan of electronics. One has to consider the residues produced in the production as well.